A federal grand jury has indicted a New Jersey man for selling over $2 million worth of Bitcoin through an unlicensed money transmitting business.

William Green, 46, who was charged with one count of operating the unlicensed business, is set to appear before a United States District Judge although no date has been set yet.
According to documents filed and statements heard in court, Green’s business was “Destination Bitcoin,” a website that allowed him to convert customers’ fiat deposits into Bitcoin in exchange for a fee.
Unfortunately for Green, US federal law says that any individual who owns or controls a money transmitting business must register it with the Secretary of the Treasury – including ones that sell Bitcoin for cash.
Green failed to do so and is now facing a maximum penalty of 5 years in prison and a hefty $250,000 fine.
Binance offering up to $290,000 bounty to catch cryptocurrency KYC extortionist
It’s never a dull day in the world of cryptocurrency, and today is no different.

Over the past few hours an unknown individual has been terrorizing cryptocurrency exchange Binance and its users by attempting to extort 300 Bitcoin (nearly $3.5 million) out of the business. The exchange is also giving a reward of up to 25 BTC ($290,000) to anyone that can help catch the miscreant.
According to an announcement from Binance , – released less than 2 hours ago – the individual claims to posses 10,000 “selfie” images that hold some similarities to the exchanges know-your-customer (KYC) data.
It seems that hundreds of the alleged KYC images have been leaked to Telegram.
https://twitterom/AndyGST1/status/1158983746890153986
Binance‘s CEO, Changpeng Zhao, tweeted shortly after saying the “KYC leak” was FUD (fear, uncertainty, doubt), a strategy used to damage the reputation of cryptocurrency businesses.
But, Binance certainly isn’t taking the accusations lightly.
The exchange has already attempted to work with the extortionist to resolve the situation. However, the unknown individual is “refusing to cooperate and [is] continuing with his extortion,” Binance‘s announcement reads.
While Binance is still investigating the legitimacy of the extortionists claims, it appears the data being used as leverage actually came from a hack that happened last year.
It seems the images being leaked are dated February 2018. During that period Binance had used a third-party provider to handle the high volume of KYC requests.
Binance says there are “inconsistencies” with the data being shared on social media to the data it holds in its systems to be compliant with KYC regulations.
The exchange says there is no evidence to suggest that any KYC images have been taken from Binance‘s systems. The images being shared on Twitter and Telegram do not have the digital watermark that is imprinted by Binance.
Binance says it’s currently investigating with the provider to find more information about the data leak.
CZ has denounced those that are further sharing the leaked images, saying they are helping and giving unnecessary attention to the situation.
The reward is being offered to anyone that is able to provide Binance with information that identifies the extortionist, and helps the exchange pursue legal action against them.
This is a developing story.
Ethereum bandit makes off with $6.1M after bypassing weak private keys
There’s a blockchain bandit on the loose – and they’ve already thieved over $6.1 million worth of Ethereum.

According to a report published by security consulting firm Independent Security Evaluators (ISE), an unknown entity has been bypassing weak private keys to swipe large amounts of Ether.
The findings show that during last year’s price rally, the stolen funds amounted to over $54 million (roughly 38,000 ETH).
As part of its investigation, ISE looked at several weak private keys, starting with simple key combinations and soon realised that associated wallets had been funnelled.
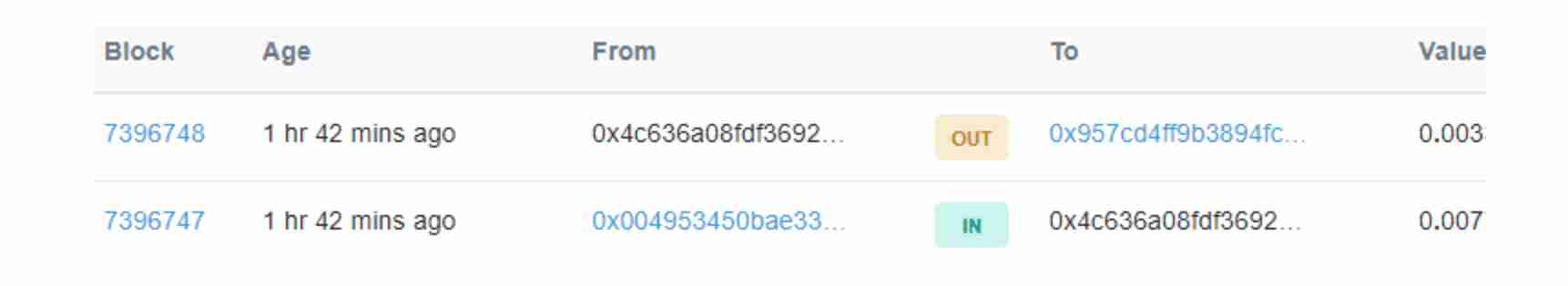
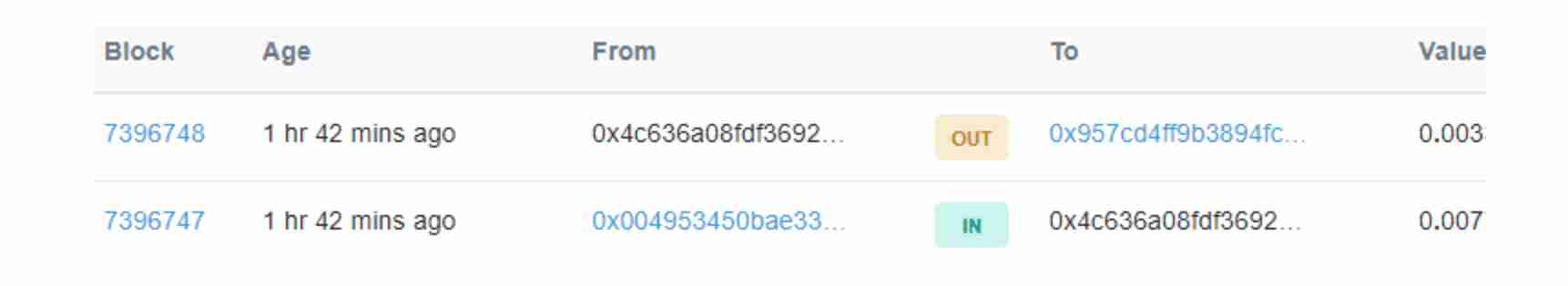
To determine the speed at which the thief was working at, researchers sent $1 in ETH to the address linked to one of the weak private keys and realised that it was “instantly” sent to another account.
“We discovered that funds from these weak-key addresses are being pilfered and sent to a destination address belonging to an individual or group that is running active campaigns to compromise/gather private keys and obtain these funds,” said the researchers.
“Blockchainbandit” as the culprit is known, is now thought to hold some $6.1 million (44,744 ETH).
“Whoever this guy or these guys are, they’re spending a lot of computing time sniffing for new wallets, watching every transaction, and seeing if they have the key to them,” ISE researcher and analyst Adrian Bednarek told Wired .
For context, private keys are a string of data, which in the cryptocurrency world, allow users to transfer funds from their wallet addresses.
The keys need to be protected at all times to avoid them becoming compromised, and to stop nefarious actors from accessing and stealing associated funds.
In this instance, weak keys could have been generated in various different ways. Researchers say they could potentially derive from a coding error which truncated what should have been a longer – and more secure – data string.
“While it is improbable that a weak key would ever be generated under legitimate circumstances using the appropriate code paths, we hypothesized that weak private keys may still be generated by coding mistakes, or operating system, device, and execution environment errors, and that these issues are common,” the report reads.
The researchers were unable to determine the thief’s identity but Bednarek told Wired he “wouldn’t be surprised if it’s a state actor, like North Korea, but that’s all just speculation.”
At the same time, it’s also worth noting that the researchers have not yet identified which wallets are associated with the weak keys, stating only that they’d been emptied.
Some question marks remain but one thing’s for sure: if the stolen funds are withdrawn and find themselves coming into the real world, the mastermind behind this criminal operation is likely to find themselves in hot water.
Did you know? Hard Fork has its own stage at TNW2019 , our tech conference in Amsterdam. Check it out .