Popular Ethereum interface and defacto token wallet MyEtherWallet (MEW) has been caught up yet another goddamn hack.

This one affects users of the Hola chrome extension, specifically those who have used MEW in the past 24 hours.
Hackers, who TechCrunch reports have utilized what “appeared to be a Russian-based IP address,” have taken over the Hola VPN service. Over five hours, MEW users who simply had the Hola chrome extension installed and running have had their wallets completely compromised.
Those affected should immediately transfer their tokens to a brand new, secure wallet .
It was only two months ago that MEW was the target of an intricate plot that saw over 215 Ethereum stolen from users wallets. That incident involved the hijacking of Amazon DNS servers, leading to the clandestine redirection of browsers to an exact replica of the MEW webpage – one specifically built to steal private keys and siphon funds.
It’s worth noting that in the three months preceding this, MEW went through an internal rift that saw the platform split in two separate entities. Literally the entire development team – bar one – suddenly up and left, launching incredibly similar Ethereum interface, MyCryptoom. Users were left wondering who the bad guy was.
While this attack may have been hard to prepare for, it is a chance to better arm yourself against phishers and scammers. Always use only approved software and official websites, even when purchasing related products such as hardware wallets – but even these can have their flaws.
The Ethereum Scam Database is one extensive resource that might prove invaluable, especially for those hunting the next great undiscovered low-cap gem.
Coinbase Pro wiped its Bitcoin to USD market clean, suspended trade for hours
Coinbase Pro has wiped one of its Bitcoin markets clean after an undisclosed issue caused trade to be suspended for hours today.
At approximately 6am PDT, Coinbase Pro reported it was investigating issues with its Bitcoin to US dollar market. Just six minutes later, the exchange warned it was necessary to cancel all live and pending orders.
Live trade was said to have resumed almost two hours later , but anyone who had orders placed or pending would inevitably have to submit them again.
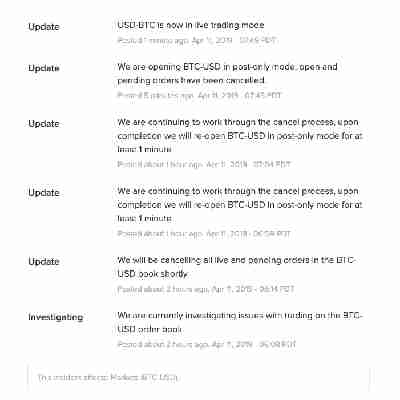
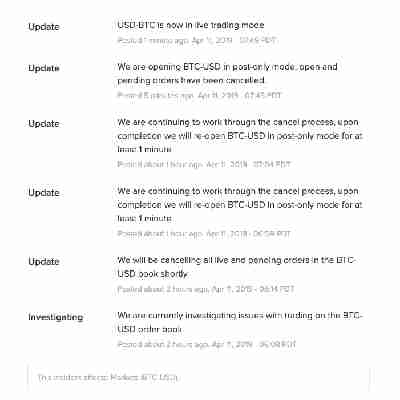
Last December, Coinbase Pro’s Ethereum markets caused a stir, as the price of Ethereum suddenly “ flash-crashed ” from $100 to $13, and climbed back to around $97 in just minutes.
Shortly after, Coinbase promised all of its platforms had been operating as planned. It also confirmed the seemingly irregular Ethereum price movement happened during “regular trading activity.”
In the case of today’s incident, though, Coinbase Pro did not provide any further details. Hard Fork has reached out to confirm the cause, and will update this piece should we receive a reply.
Update 08:07 UTC, April 12: Coinbase has since provided the following statement.
Did you know? Hard Fork has its own stage at TNW2019 , our tech conference in Amsterdam. Check it out .
Kik-approved messaging app caught storing user passwords in plain text
It appears that messaging app Blastchat – which was recently selected for Kik’s $3 million cryptocurrency developer program – has been caught storing sensitive user data, including passwords, in plain text.
Blastchat gained recognition following its inclusion the Kin Developer Program , an incubator-style startup ecosystem created by instant messaging giant Kik. The program is designed to source the best in new cryptocurrency projects by putting $3 million in incentives up for grabs.
Despite earning a spot in Kik’s developer program, Blastchat reportedly did not use any encryption for communicating between devices and (centralized) servers. This means that all passwords, emails, phone numbers, and usernames were practically visible to the creators of Blastchat.
The jarring vulnerability was first surfaced by independent outlet NuFi. Blastchat has since confirmed the issue, and quietly taken down its apps from both the App Store and Google Play.
Despite initially downplaying the authenticity of the report, a Kin spokesperson confirmed to Hard Fork that the breach is indeed authentic.
Pressed about how this flaw slipped through the Kin team, the spokesperson explained the company has a selection committee that audits the code of each applicant. Presumably, Blastchat went through the same process:
It remains unclear how many users were affected, but Kik claims Blastchat never rolled out its Kin integration. “Blastchat was never live with Kin in it,” Kin told Hard Fork. “We’ll be evaluating the security of all apps in the program before they submit the new versions with Kin integrations after the demo day.”
It should be noted that Developer Program apps submitted on demo day must be integrated with the Kin cryptocurrency. The additional pressure of protecting live money, now that Kin knows how haphazard Kin Developer Program implementations can be, has been enough to warrant the auditing of code before submission.
The whole ordeal has led to an unfortunate situation for Blastchat devs. In a tweet to Hard Fork, Blastchat described what happened after the discovery of its poor practices.
“We went and terminated our AWS Cloud instance. This removed all of [our] data, so on launch day, we will be starting with zero users,” an official account wrote. “We will have an update early next week, after we figure out what happened.”
It can’t be understated just how ludicrously negligent security practices like these actually are. The dangers of storing sensitive data in plain text files are not only widely documented, the repercussions have played out repeatedly.
If you are an early adopter of the Blastchat app, its probably best to read up on what to do, now that your account credentials have been compromised.
If anything, this is a cautionary tale for us all: partnerships are not endorsements, and if you dabble with new cryptocurrency platforms, use throwaway credentials that you don’t use anywhere else.
And for every other service on the internet: stop storing account information as plain text!